Endpoint protection: Managing and safeguarding from risks
Threat protection now requires understanding and monitoring unfamiliar threats. Utilizing Zero Trust principles, twoday helps establish a security baseline, ensuring all devices and users are authenticated and monitored for unusual behavior.

Detecting the unseen threats
Managing the unfamiliar enemyIt used to be that threat protection was about familiar threats, and antivirus was enough. Those times are gone. We need to understand that if we only look for familiar threats, we lose the fight... Today, it's about securing each device and its users in a very different threat environment, full of risks that are unknown, unexpected and unstoppable.Behavior is the key to threat detection and protection: How users and systems behave. The sign that something is wrong is unusual behavior – uncommon access patterns and locations, unexpected activities, etc. But to notice unusual behavior, you must first establish what “normal” is.
When twoday helps you with your threat identification and prevention, we use a security framework based on Zero Trust principles: Zero Trust is a security model that operates on the principle of 'never trust, always verify.' It assumes that any user, system, or service operating within or outside of an organization's perimeter could be compromised and must be authenticated and authorized before being granted access to resources. This approach helps to minimize the risk of unauthorized access and data breaches.
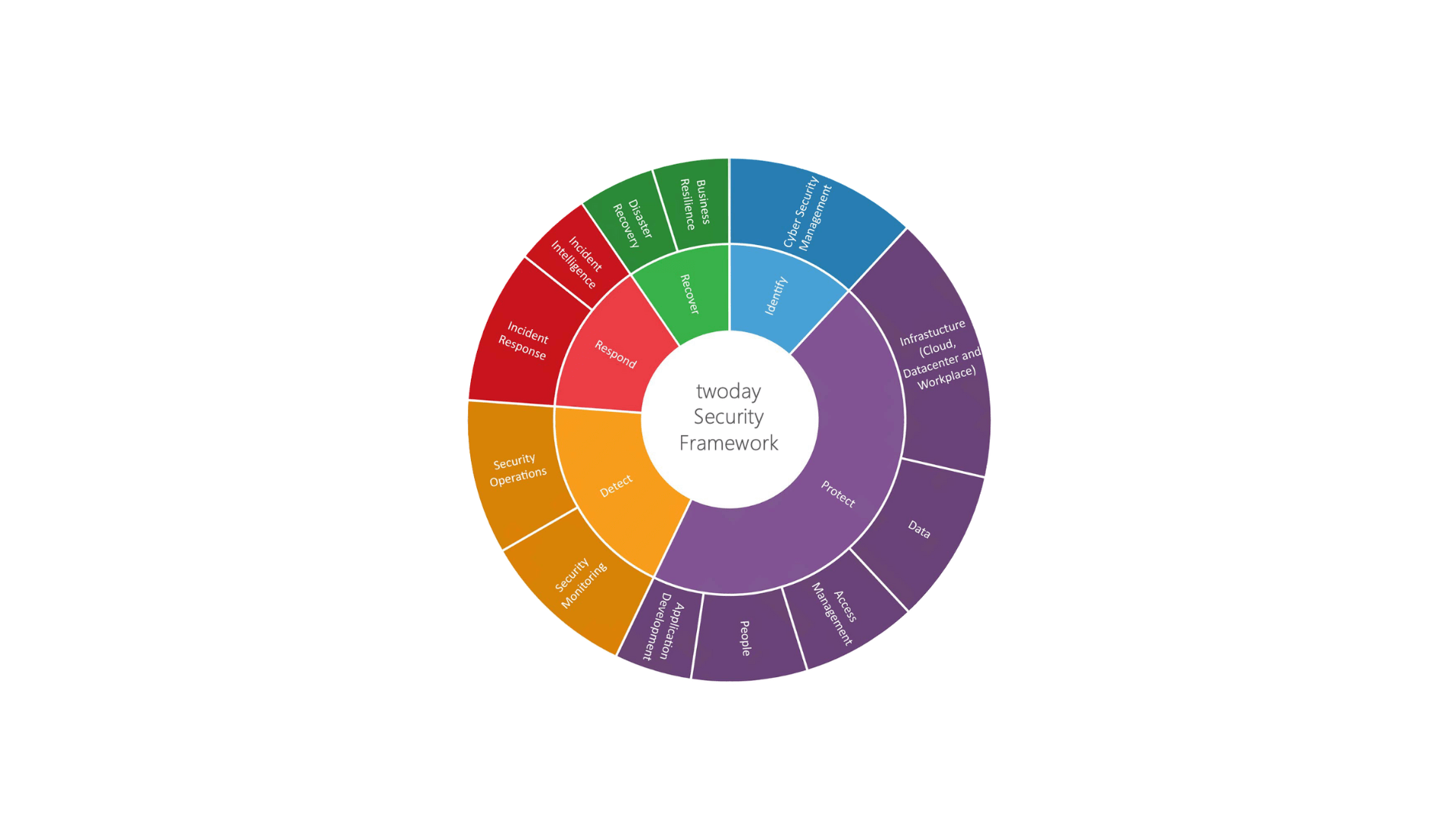
twoday security framework
- Definition of security normal baseline
- Configuration – we make sure everything is connected and working, according to best practices.
- Analysis – we evaluate your infrastructure, your business needs, and your compliance requirements, to identify the best approach for your organization.
- Visualization – every step of the way we track progress and effect, to ensure that your goals are met, and your efforts documented.

Some of the companies, we create value for
Microsoft Defender and Sentinel
Microsoft Defender for Endpoint and Sentinel are relevant products to use because they provide comprehensive and advanced protection against threats.
- Microsoft Defender for Endpoint is a powerful endpoint security solution that provides protection against various threats, including malware, phishing, and ransomware. It uses advanced behavioral analytics and machine learning to detect and respond to threats in real-time.
- Microsoft Sentinel is a cloud-native security information and event management (SIEM) solution that uses artificial intelligence to help detect, investigate, and respond to threats. It provides a centralized view of your organization's security posture, making it easier to identify and respond to threats.
Together, these products provide a robust and comprehensive security solution that helps to protect against threats and minimize the risk of unauthorized access and data breaches.
twoday are Microsoft Advanced Specialized in Threat Protection.
All our cloud- and modern work solutions are based on Zero Trust framework and philosophy. Please see our customer cases for more information.
Explore other Security and Identity topics

Data Governance and Compliance
Microsoft 365 Copilot. Before you use Microsoft 365 Copilot, you need to make sure that your organization has a strong Data Governance and Compliance framework in place.

Cloud Security
Ensure a secure and efficient cloud migration with our comprehensive security projects, leveraging best practices and advanced tools like Defender for Cloud and Microsoft Sentinel.

Identity and Access Management
Enhance your IT security with Microsoft IAM solutions. Implement effective access controls, protect user identities, and streamline identity management to mitigate cyber risks.
Get in touch
Let's assist your business with a secure strategy against threats

Casper Bernt Hansen
Business Development Manager
+45 31 90 15 29

Magnus Agervold
Head of Sales and Product Development
+45 51 57 83 32

Troels Westh
Business Development Manager
+45 31 42 01 33

Michael Skovsgaard
Business Development Manager
+45 22 10 80 45
Got questions? Reach out
Fill out the form, and we will give you a call